Company
Information Management/Quality Management
INFORMATION MANAGEMENT
Information Management
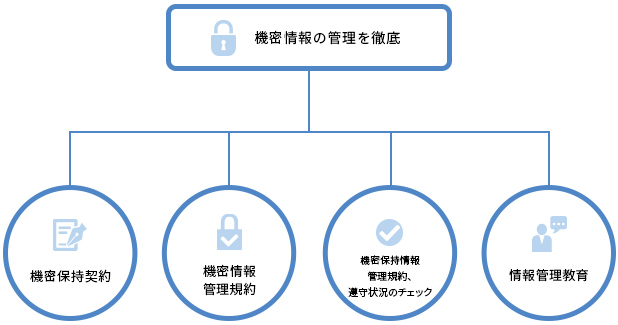
Information management structure
Human Science operates a system to manage customers' important confidential information.
The company and its employees have signed a confidentiality agreement. We have established confidential information management regulations as a policy for information management. Additionally, we check employees' compliance with these regulations every year and provide information management training annually.
We also have confidentiality agreements with our collaborating staff.
Office space access management
Entry and exit to the office floor is managed using IC cards, which only our employees possess.

Secure rooms
When creating content such as manuals for products that are not yet for sale, some work must be done in an environment where it cannot be viewed by wandering eyes. In our secure rooms, only people who are assigned to the project can enter, so the work can progress in private. To ensure that no unaffiliated persons enter, a passcode is set by those on the project.


International standard JIS Q 27001:2023 (ISO/IEC 27001:2022) certification for ISMS (Information Security Management System)
Human Science Co., Ltd. has obtained the international standard "ISO/IEC 27001:2022 (JIS Q 27001:2023)" certification for ISMS (Information Security Management System). We are still currently maintaining and operating it.

First registration date: June 18, 2012
Certification standard: JIS Q 27001:2023 (ISO/IEC 27001:2022)
Certification registration number: JP12/080233
Certification registration body (certification number): SGS Japan Co., Ltd. Certification/Business Solution Service (ISR021)
Scope:
1. E-learning production, implementation and operational support
2. Translation
3. Document/manual creation
4. Creation of AI learning data
ISMS basic policy
Establishment date: December 9, 2010
Revision date: October 24, 2023
Representative Director Tsuyoshi Kumazawa
Human Science Co., Ltd.'s corporate philosophy (value of existence) is "Human Science supports domestic and overseas companies with technology centered on technical communication and IT, and contributes to the realization of a prosperous and dream-filled society." We operate our business under this corporate philosophy and support the operations of many companies and various organizations. In doing so, we receive a large amount of information from our customers. We also handle a great deal of information about our employees and other related parties. We regard the protection of information assets as an important issue in conducting business while maintaining trust with our customers and related parties. It is essential to safely protect the information assets entrusted to us by customers and related parties to prevent incidents such as loss, theft, or unauthorized use. Therefore, we implement physical and technical security measures. It is also important that employees maintain a high awareness of information security and strive to protect information assets.
Therefore, we hereby establish our "ISMS Basic Policy" as a guideline to appropriately protect the information assets held by our company, and we will implement the Information Security Management System (ISMS) in accordance with this basic policy. All employees, including management, fully understand the intent of this basic policy and act in compliance with internal rules regarding our information security management system.
1. Definition of information security
At our company, information security is defined as maintaining the confidentiality, integrity, and availability of information assets.
2. Scope of application
Our company practices ISMS activities within the following scope.
Target business/operations: E-learning business, document solution business, localization business, annotation business, management business, sales business
Target departments: All departments (excluding CS Promotion Department and Offshore Promotion Department)
Target office: Human Science Co., Ltd. Headquarters
3. Responsibilities of Administrators
The Company appoints an information security manager who is responsible for information security. The information security manager is responsible for implementing measures to protect the Company's information assets and taking prompt action when an event that threatens information security is discovered.
4. Employee Responsibilities
Our company provides education to all employees, including temporary employees, so that everyone understands the "ISMS Basic Policy" and internal rules related to ISMS, and acts with the belief that it is their responsibility to act in compliance with the rules.
5. Identifying information assets and taking countermeasures
We identify information assets that should be protected, such as confidential information and personal information. In order to protect the identified information assets, we regularly analyze and evaluate risks and take optimal protection measures according to the risks.
6. Personal information protection
Our company will handle personal information in compliance with applicable laws, regulations, etc. regarding the personal information we handle.
7. Legal compliance
Our company promotes activities to appropriately comply with laws and concluded contracts related to information security.
8. Promotion of information security management
Our company conducts activities to maintain information security led by the information security manager, confirms that information security is maintained through audits and management reviews, and promotes continuous improvement activities for constant correction and prevention.
9. Business continuity
We will take the necessary measures to appropriately continue our important business.
Privacy policy
Revision date: November 20, 2024
Representative Director Tsuyoshi Kumazawa
Introduction
Human Science Co., Ltd. (hereinafter referred to as the "Company") protects information that can specify and identify individuals (hereinafter referred to as "Personal Information"), such as an individual's name, address, telephone number, email address, and career history, in compliance with laws and regulations and other norms related to the handling of personal information. In addition, we have established the following personal information protection policy and will continue to review and improve it in order to handle personal information assets appropriately.
Article 1: Acquisition of Personal Information
Our company properly acquires personal information without using false or other fraudulent means.
Article 2: Use of Personal Information
Our company will use personal information only within the scope necessary to achieve the following purposes of use.
If personal information is used for purposes not specified below, it will be done only after obtaining the individual's prior consent.
・Requests for estimates and responses to inquiries, as well as document delivery
・Provision of information regarding seminars and various services
・Selection and notification of results for job applicants and registered contractors, as well as content analysis
・Data retention and analysis for the improvement of our service quality and operational efficiency
・Provision of our products (including updates, troubleshooting, and support), improvements, and development
・Administrative and tax procedures related to transactions and associated operations
・Utilization of programs provided by advertising delivery companies to conduct behavior-targeted advertising on specific sites
・Analysis of attribute information and behavioral history obtained by our company to understand user preferences and tastes
・Employment management of employees and ensuring a proper working environment
Article 3 Regarding the security management of personal information
Our company will take necessary and appropriate measures to prevent the leakage, loss, or damage of personal information it handles, and to manage the safety of personal information.
Article 4 Regarding entrustment of personal information
When entrusting all or part of the handling of personal information to a third party, our company conducts a strict investigation and selection of the third party, and provides necessary and appropriate supervision over the third party to ensure the safe management of the personal information entrusted with the handling of the third party.
Article 5 Handling of personal information regarding jointly sponsored seminars
For seminars where we have specified a third party (hereinafter referred to as a "co-sponsor") with whom we are co-hosting the seminar, we may use all or part of your personal information jointly only with that co-sponsor. Personal information provided will be handled appropriately based on our "Privacy Policy".
・Scope of personal information to be jointly used
Information entered in the application form, such as name, affiliation, email address, etc.
Responses to the seminar questionnaire
・Scope of joint users
Our company and co-sponsors
・Purpose of joint use
Identity confirmation at the time of seminar registration
Seminar information/inquiry response
Announcement of events, product information, etc. provided by our company and co-sponsors
Seminar improvements
・Name of the person responsible for the management of personal data to be jointly used
Human Science Co., Ltd., Document Solution Department, Consulting Group
・How to obtain personal information
Seminar application form, seminar questionnaire (web)
Article 6: Security Measures and Use of Cookies
Our website uses cookies to enhance user convenience and collect information such as browsing history.
Cookies are a mechanism by which a web server temporarily stores data on the user's computer. This improves user operability and eliminates the need to reset settings every time the site is visited.
Furthermore, the information contained in cookies does not include any information that can directly identify the user and does not adversely affect the user's computer.
Information Provided by Cookies
We analyze the information collected using the following tools and improve our services based on the results. Information may be provided to the providers of these tools, but the use of cookies by each provider is governed by their respective privacy policies.
List of Tools Used
Google Inc.
Name: Google Analytics
Purpose: Analysis of user website usage
Privacy Policy: https://policies.google.com/privacy?hl=en
Microsoft Corporation
Name: Microsoft Clarity
Purpose: Understanding user behavior and improving services
Privacy Policy: https://www.microsoft.com/en-us/privacy/privacystatement
Google Inc.
Name: Google Ads
Purpose: Delivery of ads based on user interests
Privacy Policy: https://policies.google.com/technologies/partner-sites?hl=en
Meta Platforms, Inc.
Name: Facebook Ads
Purpose: Delivery of ads based on user interests
Privacy Policy: https://www.facebook.com/privacy/policy/
Mazrica Inc.
Name: Mazrica
Purpose of Use: Collection and analysis of user behavior logs
Privacy Policy: https://mazrica.com/legal/terms/
About reCAPTCHA
Some of our services use reCAPTCHA provided by Google to prevent unauthorized use by robots (Bots).
Information collected in connection with the use of this service is sent to Google and used for improving reCAPTCHA and for general security purposes.
By using the reCAPTCHA service, you agree to the above-mentioned purposes and data collection by Google.
User data obtained by reCAPTCHA is managed in accordance with Google's Terms of Service and Privacy Policy.
Terms of Service: https://policies.google.com/terms?hl=en
Privacy Policy: https://policies.google.com/privacy?hl=en
Article 7 Regarding provision of personal information to third parties
Our company will not provide personal information to third parties without obtaining the consent of the person in advance, except as stipulated by laws and regulations such as the Personal Information Protection Act.
Article 8 Disclosure, correction, etc. of personal information
If a person requests disclosure of his/her personal information, our company will promptly disclose it.
If we cannot confirm your identity, we will not accommodate the request to disclosure. If there is an error in the content of personal information and the person requests correction, addition, deletion, suspension of use, etc., we will investigate and respond promptly. If we cannot confirm your identity, we will not accommodate these requests.
Regarding the handling of personal information by our company, if you have any requests or inquiries as mentioned above, please contact us at the following.
[Contact information]
Human Science Co., Ltd.
Personal information inquiry desk
E-mail: privacy@science.co.jp
Phone: +81-3-5321-3111
Anonymously processed information
Our company acquires, uses, manages, and provides anonymized processed information in compliance with laws and regulations.
Items for using anonymously processed information
Still image information inside the body (intraperitoneal cavity) obtained during a surgical operation (External information such as the doctor's and patient's faces is not included. Still image metadata does not include any description that can identify a specific individual.)
Method of Providing Anonymized Processed Information
We provide the information on servers or cloud servers equipped with advanced security measures to prevent information leakage, theft, and other risks.
Quality ManagementQUALITY MANAGEMENT
ISO9001 quality policy
Established Date: August 1, 2022
Representative Director Tsuyoshi Kumazawa
1. Basic Philosophy
We are committed to supporting domestic and international companies through technology centered on technical communication and IT, contributing to the realization of a prosperous and inspiring society. To achieve this, we continuously strive for stable and improved quality by thinking together, discussing, and steadily implementing actions.
2. Quality Policy
(1) We set quality objectives to achieve this quality policy and carry out activities to accomplish them.
(2) Aiming to improve customer satisfaction, we continuously improve conformity to requirements and the effectiveness of the quality management system.
(3) All employees are aware of their respective roles and responsibilities regarding quality control and work together to implement them.
(4) This quality policy is disclosed externally through our company website.
International standard ISO 9001:2015 certification for quality management systems
Human Science Corporation has obtained certification for the international standard "ISO 9001:2015" related to quality management systems. We will continue to strive to provide services that satisfy our customers by maintaining and improving quality stability.

Language Solutions Department
Multilingual Translation Group
Certified
Applicable Standard: ISO 9001:2015
Certification Registration Number: JP23/00000014
Certification Body: SGS Japan Inc. Certification & Business Solutions Services
Scope of Registration: Provision of Translation Services
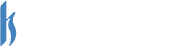
International standard ISO 17100:2015 certification for translation services
Human Science Co., Ltd. has acquired certification under the international standards that apply to Japanese-English, English-Japanese, and multilingual translation services, "ISO 17100:2015 Translation services - Requirements for translation services" (“ISO17100: 2015” for short).
ISO17100:2015 is a set of regulations for translation service providers that stipulates core processes needed to meet the demands of a high-quality translation service and the required degree of competence needed from translators and reviewers.
We will continue to strive as a team to maintain quality control in our translation projects.

Acquisition Date: November 11, 2021
Applicable Standard: ISO 17100:2015
Certification Body: Austrian Standards
Registration Number: S 001248
Scope of Certification: Translation Services

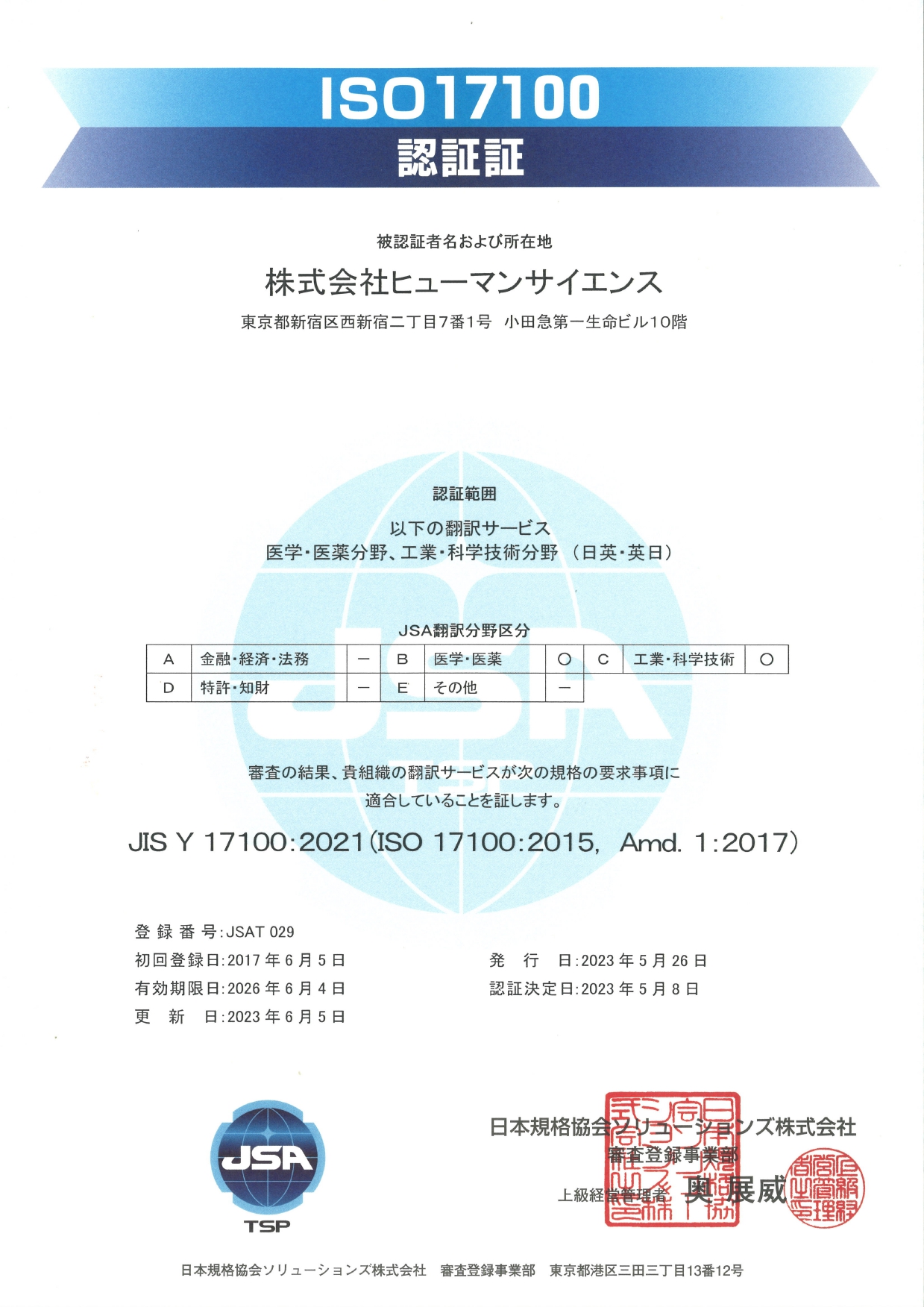
Acquisition Date: June 5, 2017
Applicable Standard: ISO 17100:2015
Certification Body: Japan Standards Association Solutions Inc.
Registration Number: JSAT 029
Scope of Certification: Translation services in the medical/pharmaceutical field and industrial/scientific technology field (Japanese-English and English-Japanese)
*Not all translation services provided by our company comply with "ISO17100".
*If you require translation services compliant with ISO17100, please inform us when placing your order.
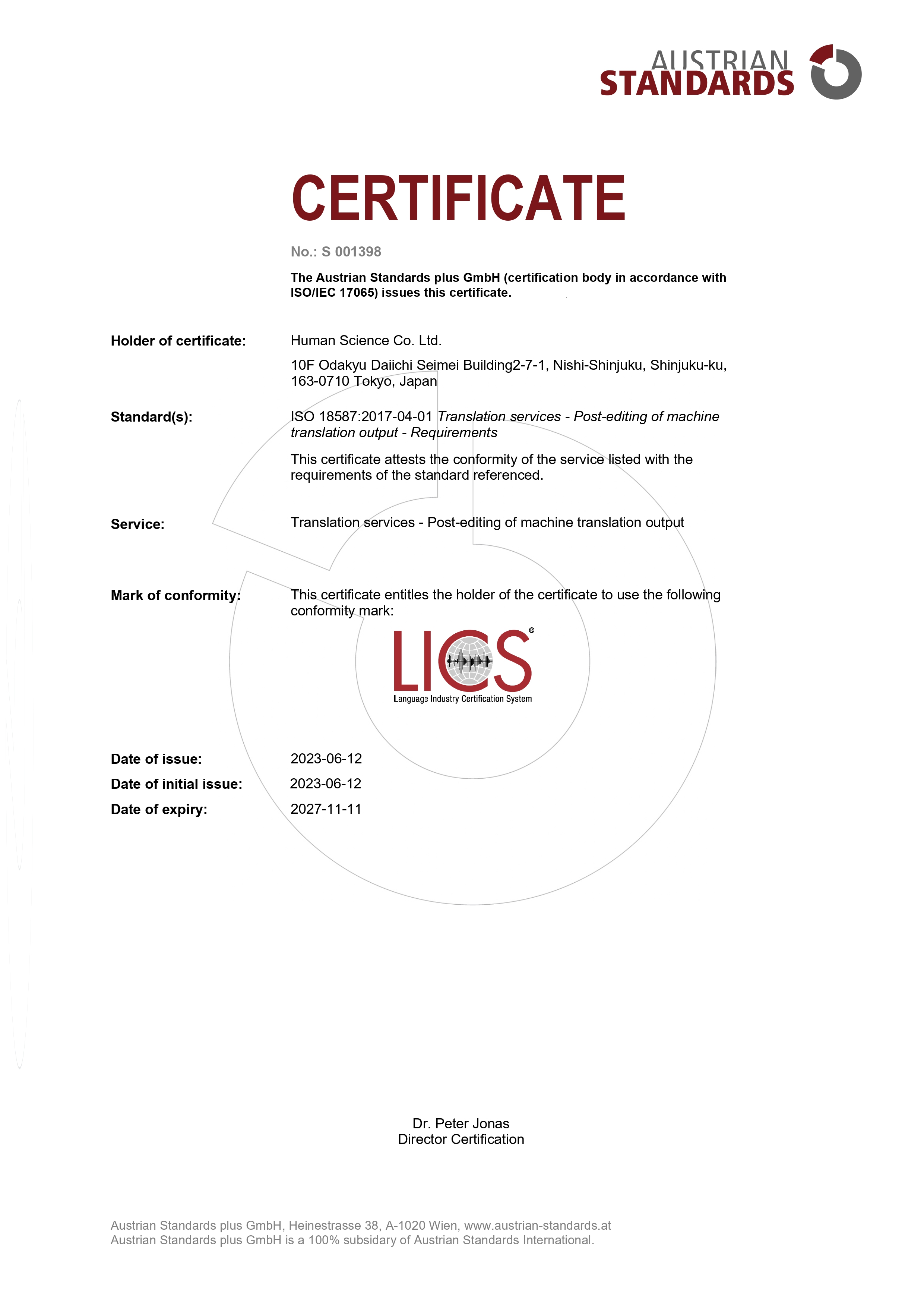
International Standard for Post-Editing
ISO 18587:2017 Certification
Human Science Co., Ltd. has obtained certification under the international standards that apply to post-editing for Japanese-English, English-Japanese, and multilingual services, "ISO 18587:2017 Translation services - Post-editing of machine translation output".
ISO 18587:2017 is a set of regulations for translation service providers that stipulates core processes needed to meet the demands of a high-quality post-editing service and the required degree of competence needed from translators and reviewers.
We will continue to strive as a team to maintain quality control in our translation projects.